Proceed as follows to create a crypto token and generate a public key in the VA Hardware Appliance. They will be used by OCSP to sign responses:
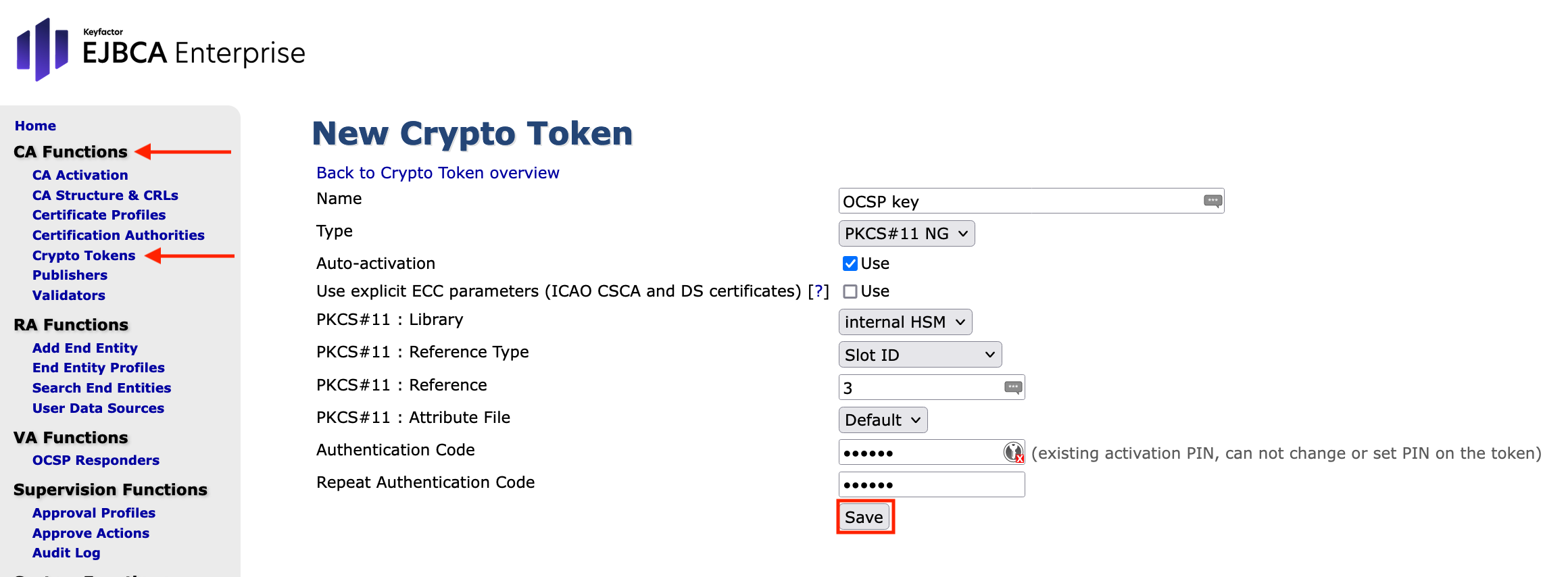
- Go to the EJBCA Enterprise Administration
- Open CA Functions > Crypto Tokens
Click Create New
Specify the following and click Save
- Name: Enter OCSP key
- Type: Select PKCS#11 NG
- Auto-activation: Enable this option
- Use explicit ECC parameters (ICAO CSCA and DS certificates): Disable this function
- PKCS#11Library: Select Internal HSM
- PKCS#11 ReferenceType: Select Slot ID
- PKCS#11 Reference: Enter 3
- PKCS#11 : Attribute File: Select Default
- Authentication Code: Enter foo123 (the previously set password).
Ensure that you have manually generated a slot password for the slot. - The index number depends on the installation.
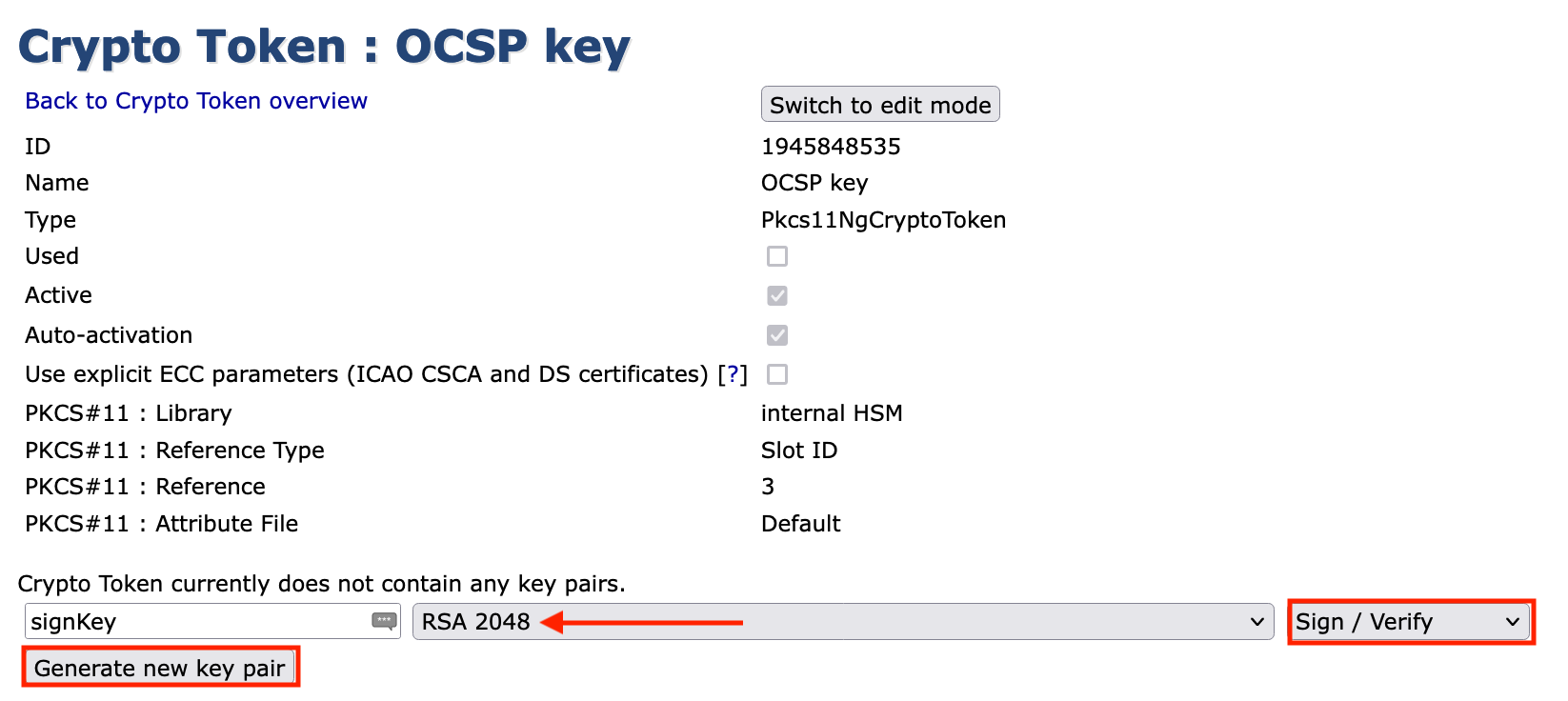
The Settings page displays the message CryptoToken created successfully.

To create the key for signing OCSP responses, specify
SignKey: RSA 2048 with the drop down function.
- -Key Usage-: choose Sign / Verify from the drop down menu
Click Generate new key pair.
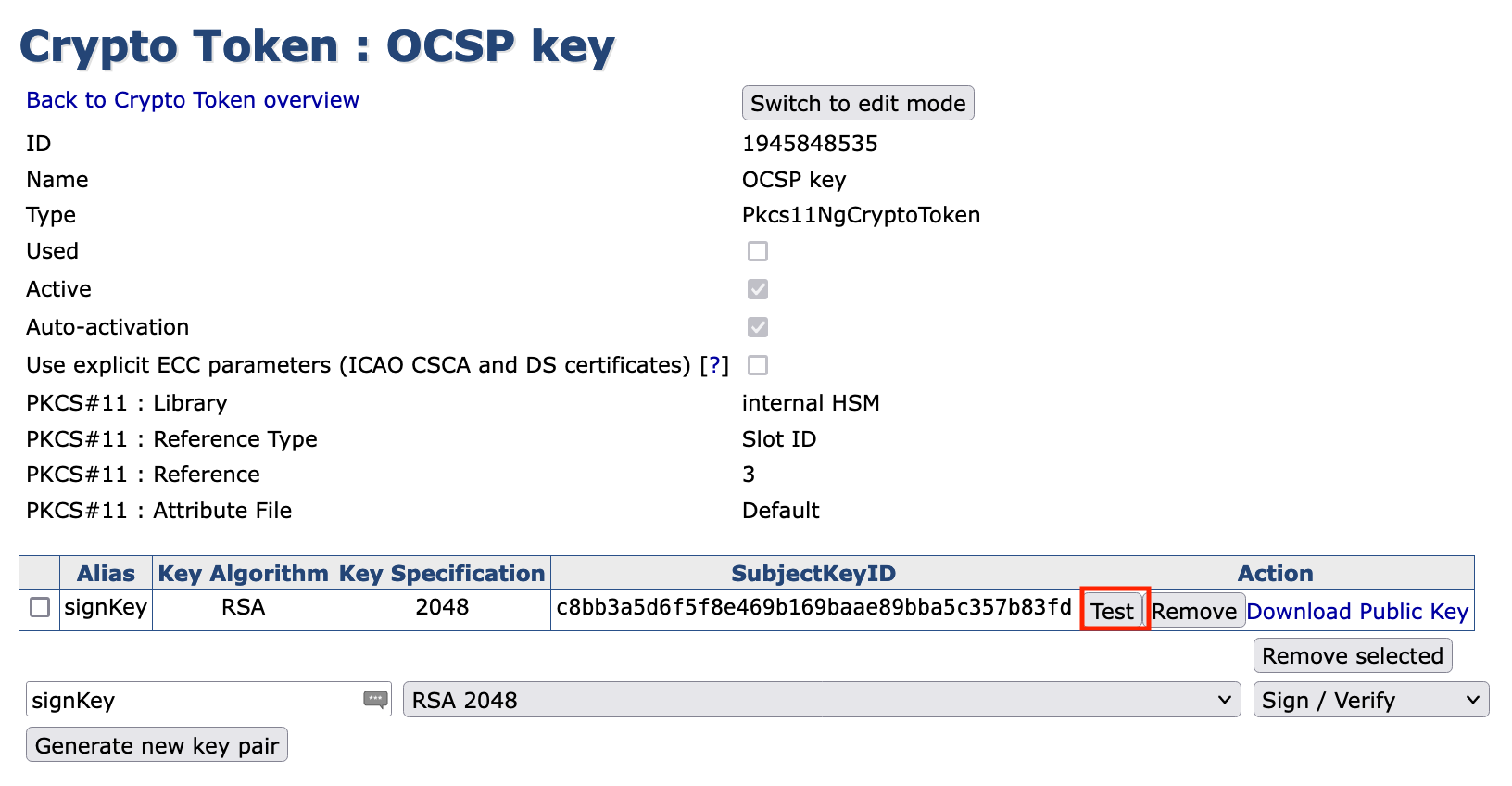
Click Test to test the key. If successful, the following message is displayed: signKey tested successfully.