Using either the command line interface (CLI) or a Secure Copy Protocol (SCP) utility, copy the file to the local system. Copy the file directly from one instance to another if VPC allows it. In this example, the file is downloaded locally and then SCP'd to the new instance.
Copy File to Local Workstation
To copy the file to the local workstation:
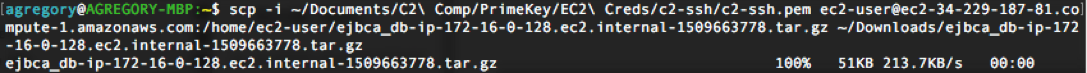
- Copy the file using the CLI:
# scp -i ~/Documents/C2\ Comp/PrimeKey/EC2\ Creds/c2-ssh/c2-ssh.pem ec2-user@ec2-34-229-187-81.compute-1.amazonaws.com:/home/ec2-user/ejbca_db-ip-172-16-0-128.ec2.internal-1509663778.tar.gz ~/Downloads/ejbca_db-ip-172-16-0-128.ec2.internal-1509663778.tar.gz
CODE
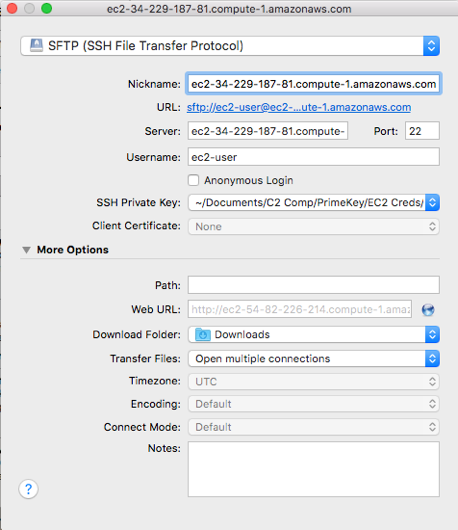
- Copy the file using a SCP utility (in this case Cyberduck):
- Specify details to connect to the instance, for example hostname, username, and SSH key:
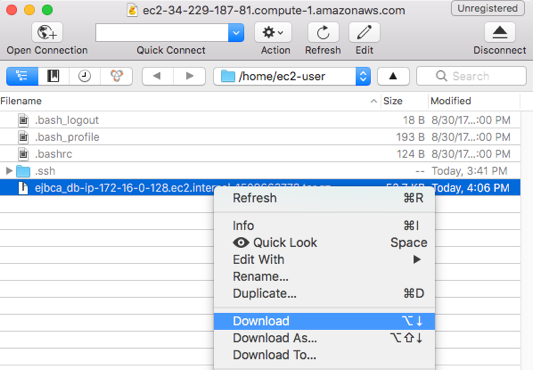
- Connect to the instance and download the file to the local system:
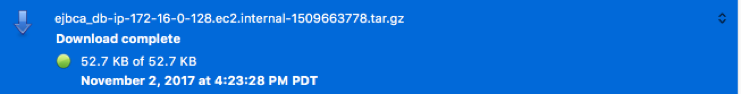
- Wait for the download to complete.
Copy Backup File to Another Instance
- SCP the backup file to another instance using the following CLI command:
# scp -i ~/Documents/C2\ Comp/PrimeKey/EC2\ Creds/c2-ssh/c2-ssh.pem ~/Downloads/ejbca_db-ip-172-16-0-128.ec2.internal-1509663778.tar.gz ec2-user@ec2-52-23-217-245.compute-1.amazonaws.com:/home/ec2-user/
CODE
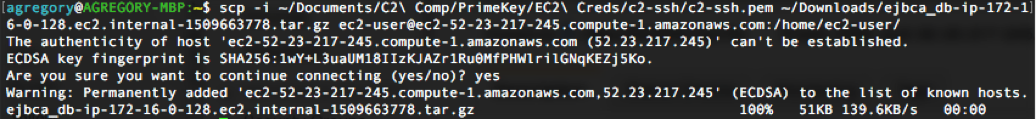
- Once the backup file is copied, SSH into the new host and verify that the file was copied correctly.