To fulfill the pending ACM PCA Certificate Request, do the following:
- Return to the AWS ACM configuration wizard.
If your console is still open to the Import a signed certificate authority (CA) certificate page, skip to step 8. Otherwise, continue.
Sign in to your AWS account and open the ACM PCA console at console.aws.amazon.com/acm-pca/home.
Choose Private CAs.
Select your private CA from the list.
Select Actions > Import CA certificate and then click Next.
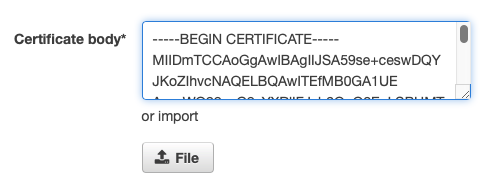
- Under Certificate body, click File and browse to the signed CA file, here previously called "AWS Corporation CA.pem".
- Review the text imported. Remove everything before -----BEGIN CERTIFICATE----- so the following text is on the first line:
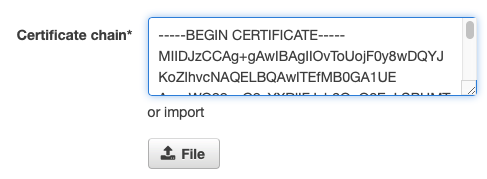
- Click File again and browse to the Root CA public certificate file, here previously called "CorporateRootCAG1.pem".
- Review the text imported and remove everything before -----BEGIN CERTIFICATE----- so the following text is on the first line:
- Click Next.
- Confirm that the certificates look correct and click Confirm and import.
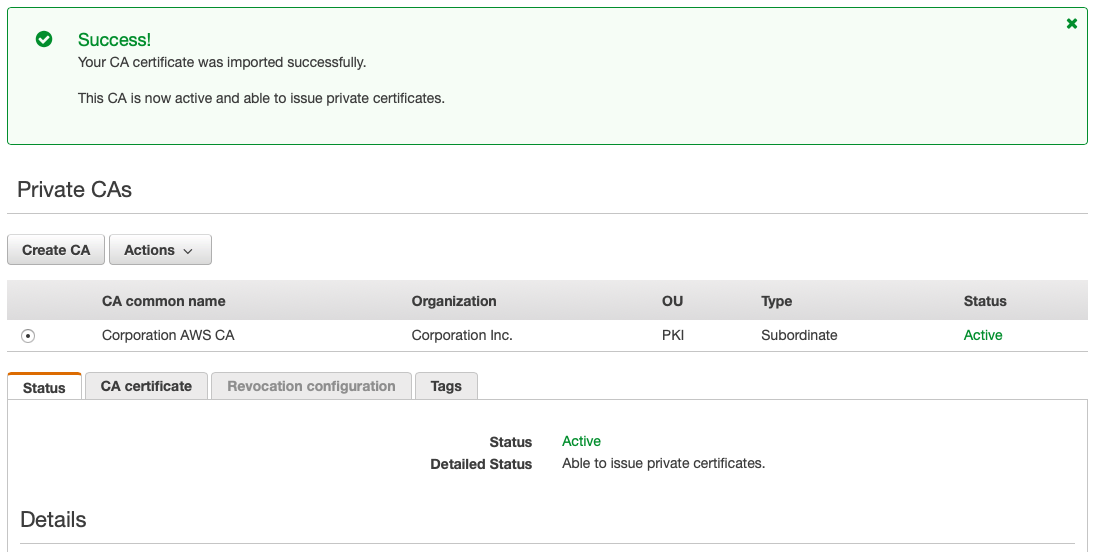
- The ACM PCA wizard returns the following success screen: