Services allow the EJBCA system to perform certain functions on a regular interval. One function is to ensure that the CRL is updated. If the CRL expires due to the validity period passing, it will be invalid.
To make sure the system generates a new CRL on a specific interval, perform the following steps:
- Under System Configuration, click Services.
- Enter the name CRL Updater in the Add Service field, and click Add.
- Select the CRL Updater service just added, and click Edit Service.
- In the Select Worker list, click CRL Updater.

- In CAs to Check, select the Corporate Root CA - G1 and Corporate Issuing CA - G1.
- In Interval, specify the desired interval. The default is 5 Minutes.
- Under General Settings, select Active.
- Click Save to save the new CRL Updater service.
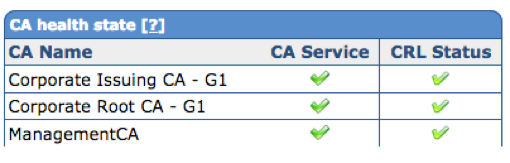
- The CA health state is now visible in the CRL Status column on the Home Screen.
’