ENTERPRISE This is an EJBCA Enterprise feature.
The following provides an overview of Microsoft Auto-enrollment and support in EJBCA.
Auto-enrollment is the method with which Microsoft Windows servers and clients provision Active Directory (AD) certificates within a Microsoft domain. Once set up in Group Policy, clients connect to a configured Certificate Enrollment Policy Server (CEP), which initially returns a set of Certificate Enrollment Policies which entitles the client to the corresponding certificates. The client then sends a request for those certificates, which is passed on to a server running Microsoft CA, which enrolls the client for the requested certificates. This process is fully oblique to the client, as are any following certificate renewals. MSAE allows Windows administrators to maintain a PKI within their domains without requiring any action from users.
eyJleHRTcnZJbnRlZ1R5cGUiOiIiLCJnQ2xpZW50SWQiOiIiLCJjcmVhdG9yTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwib3V0cHV0VHlwZSI6ImJsb2NrIiwibGFzdE1vZGlmaWVyTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwibGFuZ3VhZ2UiOiJlbiIsImRpYWdyYW1EaXNwbGF5TmFtZSI6IiIsInNGaWxlSWQiOiIiLCJhdHRJZCI6IjEwMjExNCIsImRpYWdyYW1OYW1lIjoiTVNBRSBTZXR1cCIsImFzcGVjdCI6IiIsImxpbmtzIjoiYXV0byIsImNlb05hbWUiOiJNaWNyb3NvZnQgQXV0by1lbnJvbGxtZW50IE92ZXJ2aWV3IiwidGJzdHlsZSI6ImhpZGRlbiIsImNhbkNvbW1lbnQiOmZhbHNlLCJkaWFncmFtVXJsIjoiIiwiY3N2RmlsZVVybCI6IiIsImJvcmRlciI6ZmFsc2UsIm1heFNjYWxlIjoiMSIsIm93bmluZ1BhZ2VJZCI6MTAyMTA4LCJlZGl0YWJsZSI6ZmFsc2UsImNlb0lkIjoxMDIxMDgsInBhZ2VJZCI6IiIsImxib3giOmZhbHNlLCJzZXJ2ZXJDb25maWciOnsiZW1haWxwcmV2aWV3IjoiMSJ9LCJvZHJpdmVJZCI6IiIsInJldmlzaW9uIjowLCJtYWNyb0lkIjoiYTQyM2M4Y2QtYzEyNy00NTViLWI2ODQtYjlkYjA2OGEzYjNmIiwicHJldmlld05hbWUiOiJNU0FFIFNldHVwLnBuZyIsImxpY2Vuc2VTdGF0dXMiOiJPSyIsInNlcnZpY2UiOiIiLCJpc1RlbXBsYXRlIjoiIiwid2lkdGgiOiI2MDAiLCJzaW1wbGVWaWV3ZXIiOmZhbHNlLCJsYXN0TW9kaWZpZWQiOjE3MDE3MDM2Njk2NTYsImV4Y2VlZFBhZ2VXaWR0aCI6ZmFsc2UsIm9DbGllbnRJZCI6IiJ9
The problem with this setup is that it is domain specific. In other words, this setup needs to be duplicated for each domain you have in your organization. In an enterprise environment involving hundreds of domains and tens of thousands of users, this solution does not scale.
eyJleHRTcnZJbnRlZ1R5cGUiOiIiLCJnQ2xpZW50SWQiOiIiLCJjcmVhdG9yTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwib3V0cHV0VHlwZSI6ImJsb2NrIiwibGFzdE1vZGlmaWVyTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwibGFuZ3VhZ2UiOiJlbiIsImRpYWdyYW1EaXNwbGF5TmFtZSI6IiIsInNGaWxlSWQiOiIiLCJhdHRJZCI6IjEwMjExMSIsImRpYWdyYW1OYW1lIjoiTWljcm9zb2Z0IFBLSSIsImFzcGVjdCI6IiIsImxpbmtzIjoiYXV0byIsImNlb05hbWUiOiJNaWNyb3NvZnQgQXV0by1lbnJvbGxtZW50IE92ZXJ2aWV3IiwidGJzdHlsZSI6ImhpZGRlbiIsImNhbkNvbW1lbnQiOmZhbHNlLCJkaWFncmFtVXJsIjoiIiwiY3N2RmlsZVVybCI6IiIsImJvcmRlciI6ZmFsc2UsIm1heFNjYWxlIjoiMSIsIm93bmluZ1BhZ2VJZCI6MTAyMTA4LCJlZGl0YWJsZSI6ZmFsc2UsImNlb0lkIjoxMDIxMDgsInBhZ2VJZCI6IiIsImxib3giOmZhbHNlLCJzZXJ2ZXJDb25maWciOnsiZW1haWxwcmV2aWV3IjoiMSJ9LCJvZHJpdmVJZCI6IiIsInJldmlzaW9uIjowLCJtYWNyb0lkIjoiNjk4ZmQ1YTktZDRhYS00MGFhLTgxNmMtNjYwYTM3MDRiYjE5IiwicHJldmlld05hbWUiOiJNaWNyb3NvZnQgUEtJLnBuZyIsImxpY2Vuc2VTdGF0dXMiOiJPSyIsInNlcnZpY2UiOiIiLCJpc1RlbXBsYXRlIjoiIiwid2lkdGgiOiI3MDAiLCJzaW1wbGVWaWV3ZXIiOmZhbHNlLCJsYXN0TW9kaWZpZWQiOjE3MDE3MDM2NjM2MjgsImV4Y2VlZFBhZ2VXaWR0aCI6ZmFsc2UsIm9DbGllbnRJZCI6IiJ9
This is where EJBCA becomes your solution - by using the EJBCA CA instead of the Microsoft CA and configure the client to connect directly to EJBCA RA machines instead of a Microsoft Certificate Services, a single EJBCA CA can serve your entire Microsoft PKI through RA instances.
eyJleHRTcnZJbnRlZ1R5cGUiOiIiLCJnQ2xpZW50SWQiOiIiLCJjcmVhdG9yTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwib3V0cHV0VHlwZSI6ImJsb2NrIiwibGFzdE1vZGlmaWVyTmFtZSI6IkFubmljYSBXYWx0ZXJzc29uIiwibGFuZ3VhZ2UiOiJlbiIsImRpYWdyYW1EaXNwbGF5TmFtZSI6IiIsInNGaWxlSWQiOiIiLCJhdHRJZCI6IjEwMjEwOSIsImRpYWdyYW1OYW1lIjoiTWljcm9zb2Z0IFBLSSB3aXRoIEVKQkNBIiwiYXNwZWN0IjoiIiwibGlua3MiOiJhdXRvIiwiY2VvTmFtZSI6Ik1pY3Jvc29mdCBBdXRvLWVucm9sbG1lbnQgT3ZlcnZpZXciLCJ0YnN0eWxlIjoiaGlkZGVuIiwiY2FuQ29tbWVudCI6ZmFsc2UsImRpYWdyYW1VcmwiOiIiLCJjc3ZGaWxlVXJsIjoiIiwiYm9yZGVyIjpmYWxzZSwibWF4U2NhbGUiOiIxIiwib3duaW5nUGFnZUlkIjoxMDIxMDgsImVkaXRhYmxlIjpmYWxzZSwiY2VvSWQiOjEwMjEwOCwicGFnZUlkIjoiIiwibGJveCI6ZmFsc2UsInNlcnZlckNvbmZpZyI6eyJlbWFpbHByZXZpZXciOiIxIn0sIm9kcml2ZUlkIjoiIiwicmV2aXNpb24iOjAsIm1hY3JvSWQiOiJiY2NjNjliYy03MjNlLTQzMDQtOWE5Mi05MWJiMWIyMzJkMzciLCJwcmV2aWV3TmFtZSI6Ik1pY3Jvc29mdCBQS0kgd2l0aCBFSkJDQS5wbmciLCJsaWNlbnNlU3RhdHVzIjoiT0siLCJzZXJ2aWNlIjoiIiwiaXNUZW1wbGF0ZSI6IiIsIndpZHRoIjoiNDAwIiwic2ltcGxlVmlld2VyIjpmYWxzZSwibGFzdE1vZGlmaWVkIjoxNzAxNzAzNjU5NzU3LCJleGNlZWRQYWdlV2lkdGgiOmZhbHNlLCJvQ2xpZW50SWQiOiIifQ==
Microsoft Auto-enrollment Key Archival
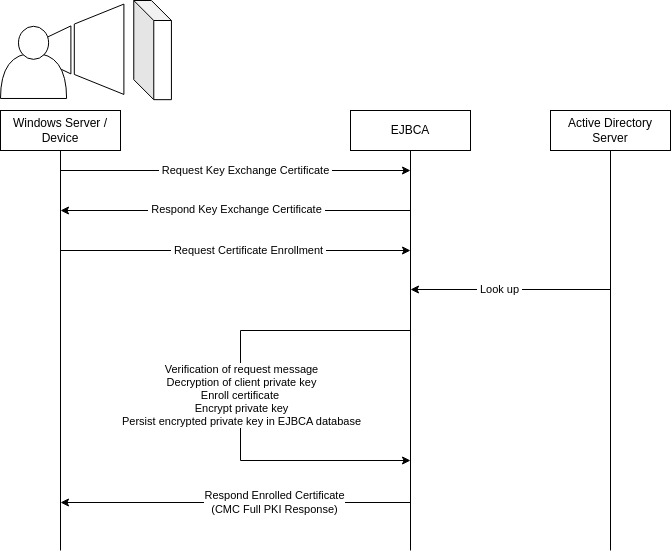
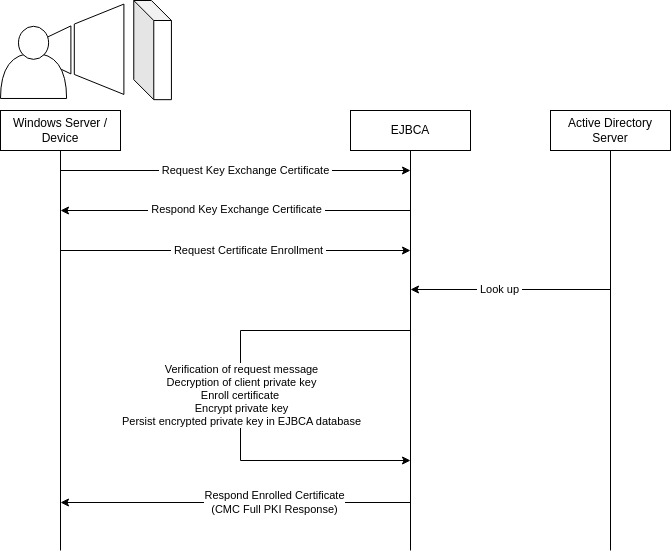
As of 8.2, EJBCA supports key archival and recovery for Microsoft auto-enrollment. By default, EJBCA stores encrypted keys in the database and enables administrators to retrieve keys in case a private key is lost. Microsoft auto-enrollment key archival is configured in the Windows server certificate template and in EJBCA's system configuration, auto-enrollment alias, and end entity. For more information on how to configure auto-enrollment in EJBCA, see Microsoft Auto Enrollment Configuration, and for more information about how to recover the private key, see Key Archival: Recovery.
Only RSA keys are supported for archival and recovery.
To enhance security, a CA Administrator role can be assigned for key recovery and a CA Administrator can for example be configured to have the capability to recover a key for a specific end entity profile only. For more information on how to create a CA Administrator role, see Roles and Access Rules Operations. Additionally, you can configure an approval mechanism to ensure that a key recovery is approved by several administrators. EJBCA provides two types of approval profiles, Accumulative and Partitioned, see Approvals.