SignServer Introduction
SignServer is a framework designed to perform different kinds of digital signatures for different applications.
SignServer digitally signs your documents, code, time-stamping, and ePassports. It keeps signature keys secure, and your workflows easy, secure and auditable.
- Code Signing: MS Authenticode, Java including Android APK and Generic.
- Document Signing: PDF, XML, XAdES (BES and T).
- Time-stamping: RFC 3161 and MS Authenticode time stamps, ETSI compliant.
- ePassports: ICAO compliant MRTD signer.
SignServer is a server-side signing server with plug-ins for different signature types. Signature keys are kept secure on the server-side, preferably using a Hardware Security Module (HSM), and users are authenticated to perform signatures online.
One instance of SignServer can host multiple use cases/signers, organizations and users. Multiple Signers and Validators serve all your digital signature needs within one instance of SignServer.
Instead of managing a myriad of distributed signing islands where each team has its own solution, using a central signing solution simplifies administration, improves security and lowers cost.
Code Signing
SignServer is a secure code signing solution that allows you to keep code signing keys protected, and also provides a centrally managed and audited single service for all your code signing needs and allows you to keep code signing keys protected.
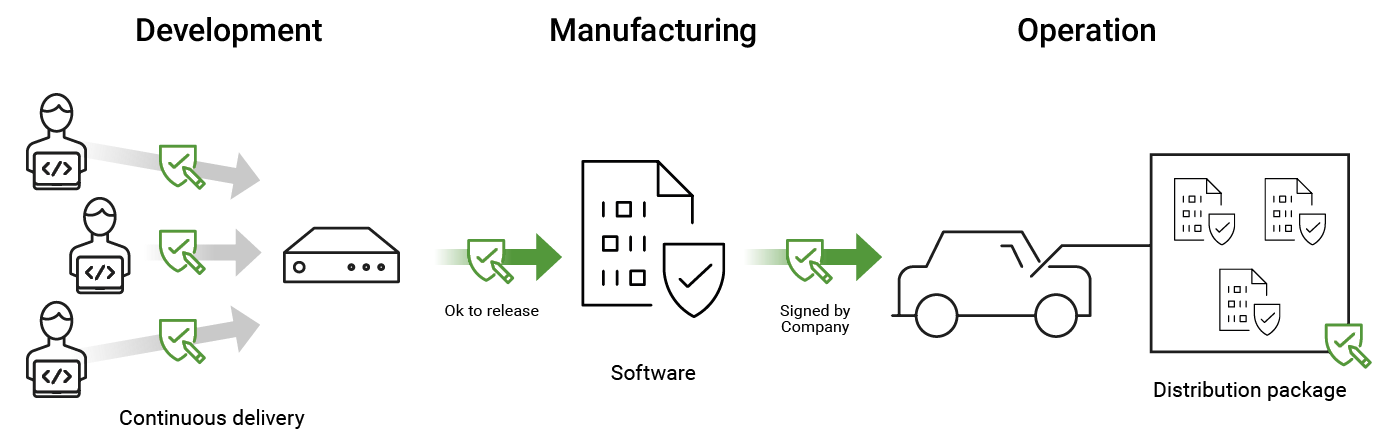
SignServer enables different project members or systems to authenticate and share the same protected code signing key and certificate when signing, and also provides audit records of who signed what. SignServer can also control individual code signing keys where only one person is granted authorization.
Most code signing needs are fulfilled by SignServer using different signers and custom plug-ins:
- Authenticode for Portable Executables (PE signing) and Windows Installer (MSI signing).
- Java (JAR signing).
- PGP signing.
- Client-side hashing and construction for Authenticode, JAR, and PGP signing.
Document Signing
SignServer allows signing any digital document and is designed to perform automated signatures and other cryptographic operations on digital documents. SignServer can easily be adapted to customer-specific needs by using plug-ins and supports document signing formats such as PDF (ISO 32000), XAdES-BES, XAdES -T, XMLdSig, CMS/PKCS#7, and Plain (PKCS#1, etc.)
PDF Signer
The SignServer PDF signer adds server-generated digital document signatures to PDFs and includes support for visible signatures, different certification levels, and requesting and embedding times-tamp responses, CRLs, and OCSP responses.
The flexible authorization system provides control of who is allowed to sign documents, and the PDF signer is thus ideal for organizationally authenticated documents such as receipts, invoices, regulatory documents and supports long term archival.
Time-stamping
Time-stamps are generally used together with eSignatures to provide proof that a document existed before a certain time, and can also be used together with advanced signatures to ensure long-term validation of archives.
SignServer can be used as the time stamp unit within a Time Stamp Authority (TSA) to generate digitally signed time stamps and includes monitoring of time synchronization, offering both RFC 3161 and MS Authenticode time-stamps.
- Configurable time sources.
- qcStatements extension support for Qualified Electronic time-stamps according to the EU Regulation No 910/2014 (eIDAS).
- SignServer TimeMonitor application and modules for monitoring time synchronization in TSA set-ups.
ePassports
SignServer includes a built-in plug-in for Machine Readable Travel Document (MRTD) signing. MRTD is implemented worldwide within electronic passports mandated by ICAO.
SignServer is used both for MRTD signing and for CSCA master list signing:
- Electronic ePassport document signing (MRTD) compliant with ICAO requirements:
- LDS version 1.8 support.
- Support for limiting the number of signings.
- Support for key usage period.
- Multiple active logical signers with fail-over when the sign limit is exceeded or the key usage period expires.
- Signer suitable for signing ICAO Deviation/Defect Lists.
- ePassport CSCA master list signer compliant with ICAO requirements.