When accessing the Keys tab in Azure Key vault, you may get an error that says:
To get around this, perform the following steps to configure Azure Key Vault firewalls to allow access to your key vault.
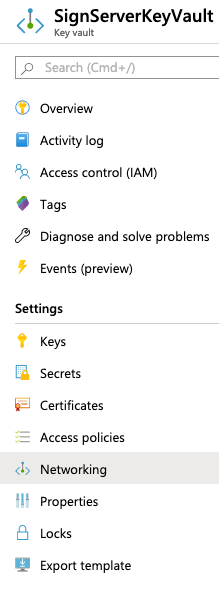
- Browse to the Key Vault that SignServer is using, in this example SignServerKeyVault, and select Networking.
- Add your public IP into the Firewall section on the Firewalls and virtual networks tab. To allow a single IP, end the IP with /32. Otherwise, add your appropriate subnet.
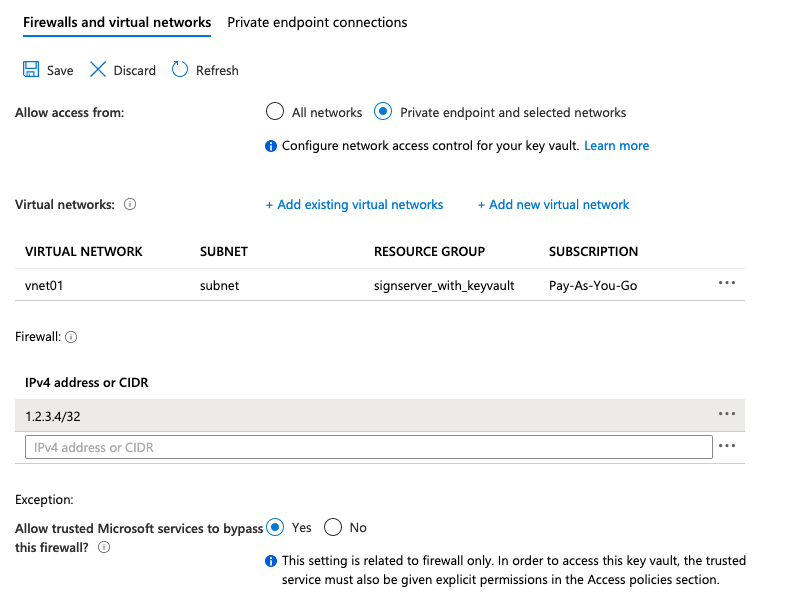
- Click Save.
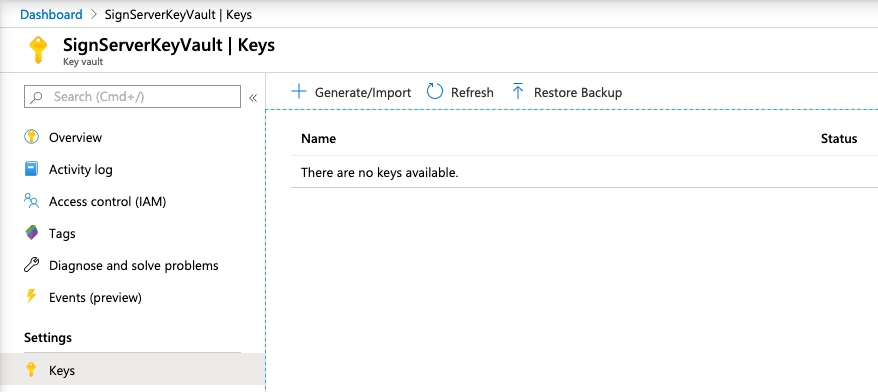
- You will now be able to access all of the keys on the Keys tab of the Azure Key Vault.
Next, continue with creating a test key that SignServer can use to activate the Crypto Token, see Creating First Key for SignServer.