CA Operations Guide
This page provides guide and information on setting up Certification Authorities, profiles and general configuration of an EJBCA instance.
For more information on RA Management tasks, see the RA Operations Guide and for information on EJBCA concepts and configuration, see the EJBCA CA Concept Guide.
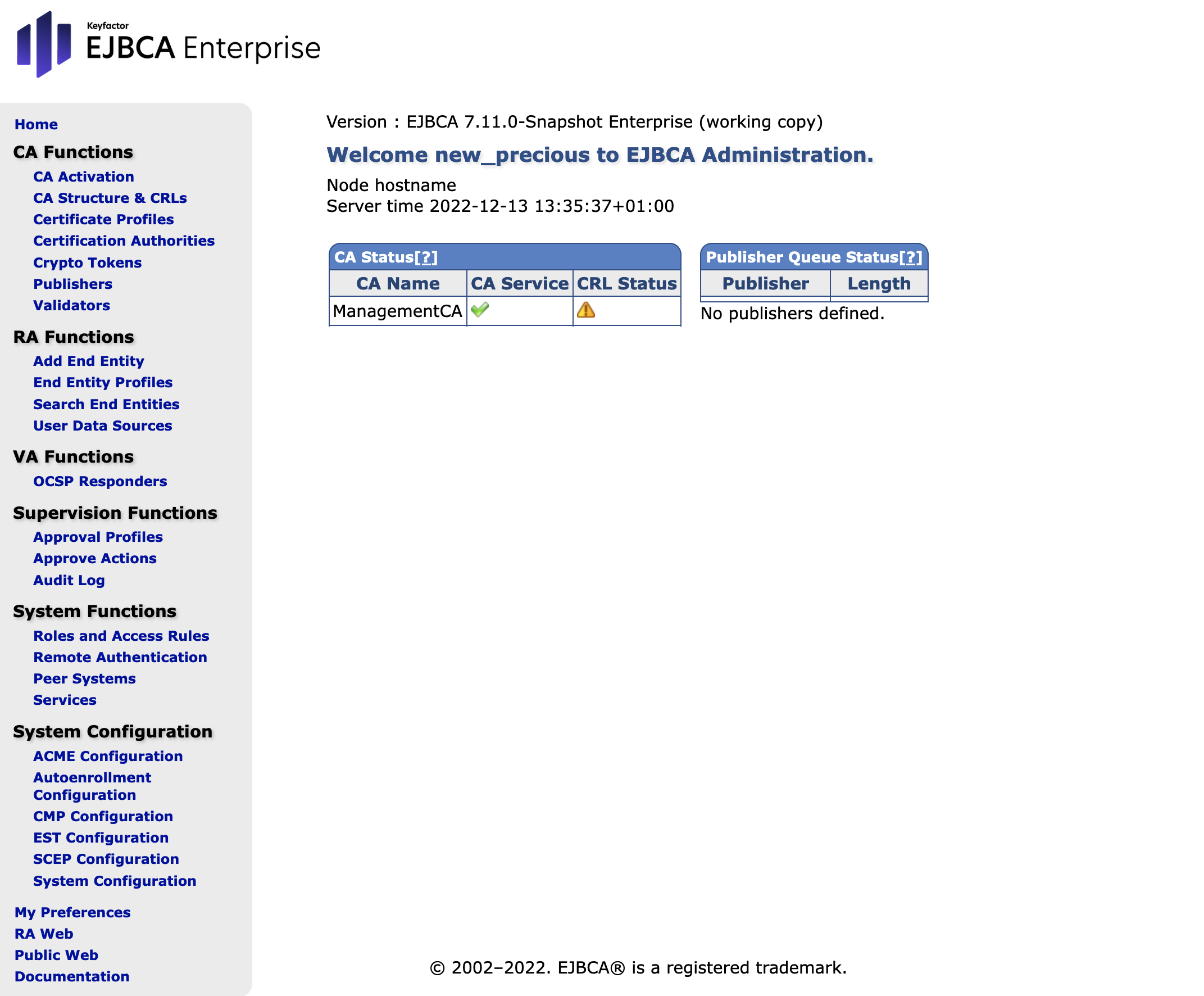
Overview Page
The first page you'll be greeted with in the CA UI is the Overview Page, which gives some general information about the status of this EJBCA instance.
CA Management
Managing X509 CAs
A Certification Authority (CA) issues certificates to and vouches for the authenticity of entities.
→ For information on managing CAs and instructions on how to create, renew, revoke, and import and export Certification Authority (CAs), see Managing CAs.
For workflows describing how to perform CA Management operations, see the following pages:
→ Creating an Issuing CA Signed by an External Root
Managing CVC CAs
Card Verifiable Certificates (CVC) are used by EU Extended Access Control (EAC) ePassports and eIDs. CVC CAs differ from the standard x509 CAs in some ways.
→ The Managing CVC CAs page covers these differences.
For workflows describing how to perform CVC CA Management operations, see:
→ Creating a DV CA and Issuing Inspection System Certificates
Crypto Tokens
In EJBCA, cryptographic keys are stored in a Crypto Token. A Crypto Token can either be stored in a database, known as a soft Keystore, or on a Hardware Security Module (HSM).
→ For information on managing crypto tokens, with instructions on how to create, edit, and activate crypto tokens, see Managing Crypto Tokens.
Certificate Profiles
A Certificate Profile defines the constraints of the certificate, for example, what keys it can use, and what the extensions will be.
→ For information on how to create and edit Certificate Profiles, see Managing Certificate Profiles.
For workflows describing how to setting up various common Certificate Profiles, see the following pages:
→ Create a Certificate Profile for SSL Servers
→ Create a Certificate Profile for a Document Signer for Passports
→ Import/Export Certificate Profiles
End Entity Profiles
End Entity Profiles allow narrowing down and automatically input some variables used in the certificate.
The End Entity Profile is used together with the Certificate Profile to create the certificates signed by the CA. The Certificate Profile defines the constraints of the certificate, for example what keys it can use and what the extensions will be, while the End Entity Profile defines the information in the certificate, for example country and organization.
→ For more information on importing and exporting End Entity Profiles and instructions for creating a Server End Entity Profile, see End Entity Profile Operations.
OCSP Management
→ For information on managing an OCSP Responder, whether situated locally on the same machine as the CA or remotely on a VA, see OCSP Responder Management.
Roles and Access Rules
→ For information on working with roles and access rules, see Roles and Access Rules Operations.
CA Operations Guide Topics
The full list of operations guide topics are as follows:
Workflows
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page:
-
Page: