To establish the connection to the Hardware Appliance, you must verify the TLS certificate by confirming the TLS fingerprint.
To do this, you need the TLS fingerprint as described in Step 2: One Time Password and TLS Fingerprint.
Connect to the Hardware Appliance:
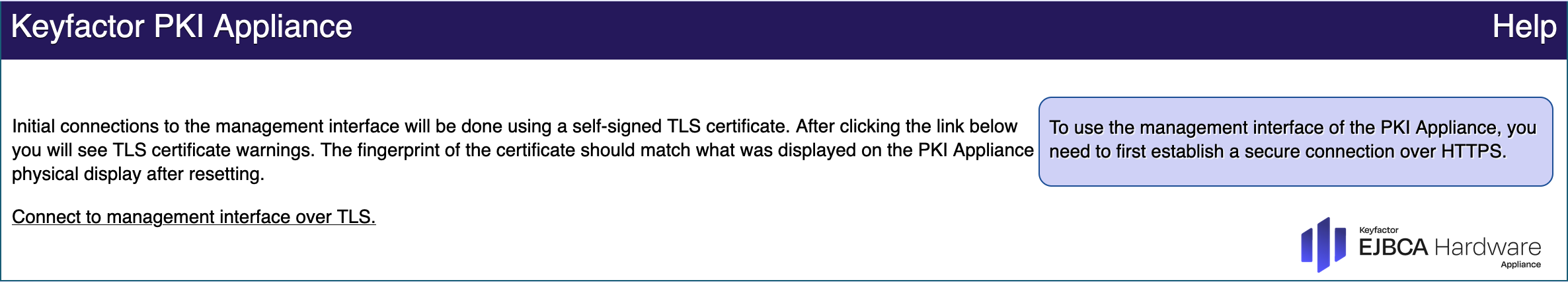
Open your browser and enter the IP address of the Management Interface.
You have assigned this address in Step 3: Changing the IP Address of the Hardware Appliance.
Click Connect to management interface over TLS:
Your browser will prompt you to select a certificate.
Click Cancel. The dialog Potential security risk ahead opens.
- Click Advanced. An info box on the certificate requirements opens.
Click Accept the risk and continue. You will return to the WebConf page Verify TLS Certificate:
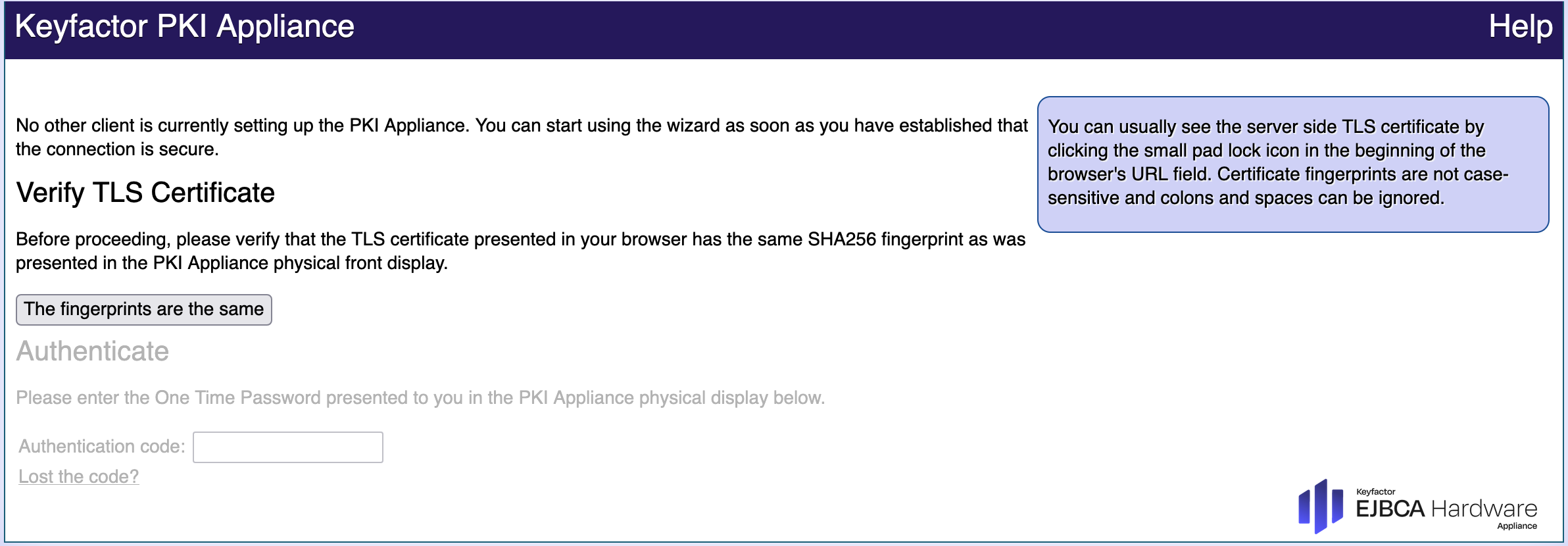
Check the fingerprint of the TLS certificate and compare it to the TLS fingerprint of the Hardware Appliance:
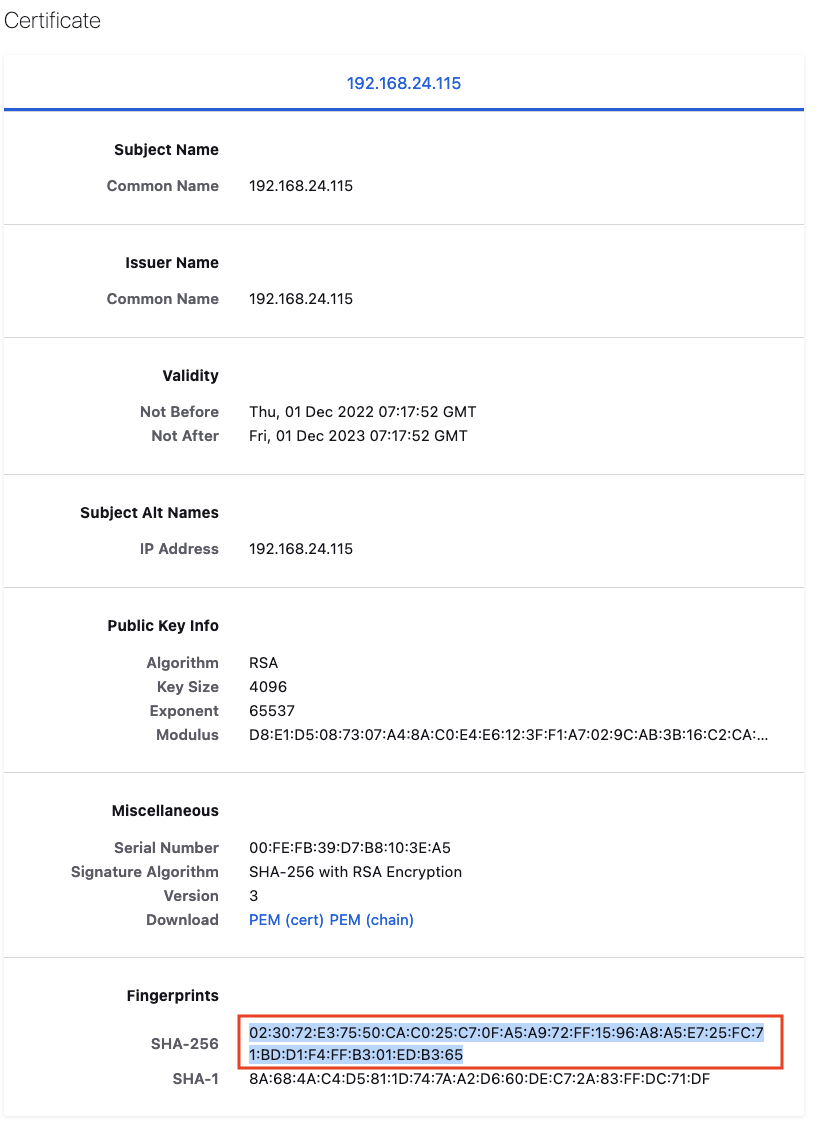
Click the Padlock icon  in the address bar of your browser.
in the address bar of your browser.
Click > to expand the information for Connection is Not Secure. This opens information on the security of your connection.
Click More Information and then View Certificate to open the Certificate Viewer.
In the Certificate Viewer, find the SHA256 Fingerprint and compare it to the TLS fingerprint of the Hardware Appliance.
If the two fingerprints match, the Hardware Appliance is connected to the correct machine.Close the Certificate Viewer panel.
- Click The fingerprints are the same in the Hardware Appliance certificate verification page (see Verify TLS Certificate).
The Authenticate page will open and you can proceed with Step 5: Running WebConf Wizard.